There are several challenges that emerge when it comes to digitalizing the global healthcare landscape. While the benefits can be significant, dealing with the potential security concerns has emerged as a major challenge for healthcare organizations worldwide. The COVID-19 pandemic, especially, has posed a major challenge for the resilience and capabilities of the global healthcare industry. From personal diagnostics, medical devices, providers and OEMs have had to step up their activities and operational paradigms to address the emerging requirements
The digitalization journey involves several key challenges around ensuring security for healthcare data. Data security has emerged as a major concern for the healthcare industry today. The large volumes of sensitive personal information available with medical organizations and device manufacturers make them the major targets, and most of them continue to lack the necessary tools and expertise to protect against potential challenges.
The recent global surge in cybercrimes has led to many healthcare organizations realizing that they require a revamped cybersecurity paradigm. On the whole, while the industry is now starting to realize the requirement for updated data security, challenges persist.
Worldwide, the medical industry, riddled with legacy systems and solutions, is one of the most attractive targets for cybercriminals. Medical organizations today face more pressure than most to improve the security of their data and digital assets. These businesses are a favorite target of cybercriminals, and as long as they handle valuable data, they will continue to be so.
The need, therefore, boils down to enhanced application and implementation of cybersecurity measures and policies. It's not just about guarding against attacks or preventing breaches; it's also about minimizing the potential damage caused by a successful attack.
While the global medical industry today realizes the emerging and urgent need for ensuring data security, several obstacles persist. Here are some of the key hurdles that we envisage:
- Ransomware Attacks
Ransomware incidents plagued leading hospitals worldwide during 2020, and even in 2021. Unless we make the necessary changes now, 2022 could be worse. About a third of major global healthcare organizations have already suffered a ransomware incident in 2020 alone, and two-thirds of those incidents have been successful.
- Threat to Mobile Applications
A major threat to the healthcare data security paradigm lies in the mobile medical applications ecosystem. With telehealth adoption skyrocketing – rising by 50% in Q1 2020 alone, helping make health care increasingly accessible – new risks have continued to emerge. Sensitive medical information is increasingly accessible through smart mobile devices, which, unfortunately, often do not have an adequate security coverage.
- IoT Vulnerabilities
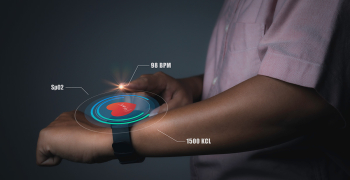
Another key technology trend with potentially troubling cybersecurity implications is the growing Internet of Things (IoT) adoption across the healthcare continuum. While many healthcare organizations worldwide have embraced the benefits of the IoT ecosystem to streamline their operations and improve upon data reporting, these devices are often left vulnerable in the absence of adequate cybersecurity measures.
- Interoperability Challenges
As hospitals ideate, integrate, and embrace a greater quantum digital services, interoperability could become a challenge. Most electronic health record (EHR) solutions today feature proprietary capabilities and features that could stymie as streamlined communication with similar (and relevant) systems – potentially causing delays or even errors, exposing sensitive data to unauthorized access.
- Software / Hardware supply chain vulnerability
Companies integrate a wide variety of third-party system libraries and vendor supplied hardware to achieve seamless connectivity. These introduce a newer variety of security vulnerabilities in the system. The vendor supplied components and libraries should be assessed for security flaws. There should be a shared responsibilities approach in place to validate the modules.
Vendors must own the security of the elements before integration while companies must own the overall security of the devices and platforms after integration.
At LTTS we share our collective insights into how we are addressing these challenges across the digital product portfolio for our customers by leveraging an integrated approach that combines together data protection services with endpoint protection solutions for complete visibility into user behavior across all devices. Find out more today.